
Schmidt-Cassegrain telescopes (often referred to as SCTs) and Maksutov-Cassegrain telescopes (often referred to as MCTs, Maksutovs, or Maks) are popular telescope designs originating in the last century, commonly marketed to beginners and experienced astronomers alike as compact, low-maintenance, portable, and versatile telescopes for a variety of uses.
Both telescope designs are similar in basic optical design and manufacture but differ dramatically in their design goals and real-world usage. The facts about them are also often distorted heavily by marketing hype, outdated advice, or bias in astronomy circles, making it even harder to understand the advantages, disadvantages, and differences between Schmidt-Cassegrain and Maksutov-Cassegrain.
- A Comparison Between SCT and Maksutov
- What is a Schmidt-Cassegrain telescope (SCT)?
- Key advantages
- Key disadvantages
- The Start: Classical Cassegrain Telescopes in 1600s
- The Dall-Kirkham Alternative
- The Schmidt Camera and Its Influence
- The Birth of the Schmidt-Cassegrain
- Focusing Mechanism and Related Optical Challenges
- Common Optical Issues in Schmidt-Cassegrains
- Thermal Management and Dew Control
- What is a Maksutov-Cassegrain telescope (MCT)?
A Comparison Between SCT and Maksutov

| Schmidt-Cassegrain | Maksutov-Cassegrain | |
| Apertures usually available | Generally 6-14” but as small as 4” and sometimes up to 22” in rare samples | 4-7”, sometimes up to 10” if you pay enough |
| Best for | Astrophotography | Visual astronomy |
| Astrophotography | Anything | Planets/moon only |
| Central obstruction by diameter | 33-40% | 25-35% |
| Resolution/sharpness comparable to | Refractor 2-3” smaller Reflector 1-2” smaller MCT 1-2” smaller | Refractor 1-2” smaller Reflector at the same size SCT 1-2” bigger |
| Overall system efficiency vs. refractor, Newtonian reflector | ~80% ~94% | ~85% ~99% |
| Price/in^2 of aperture | Average $20 ($18-$22) | Average $28 ($25-$31) |
What is a Schmidt-Cassegrain telescope (SCT)?
Key advantages
- Can usually be converted to f/2 Schmidt cameras or f/6.3 photographic systems for deep-sky astrophotography.
- Lighter weight than Maksutov-Cassegrains.
- Faster cooldown than Maksutov-Cassegrains
- Cheaper than Maksutov-Cassegrains
- Faster focal ratio and thus wider field than most Maksutov-Cassegrains.
- Available at large apertures.
Key disadvantages
- Large central obstruction, inherent design flaws, and quality control issues lead to below-average image quality at any aperture
- Many old scopes compromised in optical quality
- Fragile
- Hard to collimate accurately; almost impossible to collimate without actually pointing at a star at night
SCTs are usually available at apertures of between 6” and 14”, but older models such as Celestron’s semi-retired C5, the 4”, 16” and 20” scopes by Meade, and the legendary Celestron C22 (ironically their debut product) exist as well.
The Start: Classical Cassegrain Telescopes in 1600s
A Schmidt-Cassegrain telescope is a variation on the Cassegrain telescope design, invented in the late 1600s.
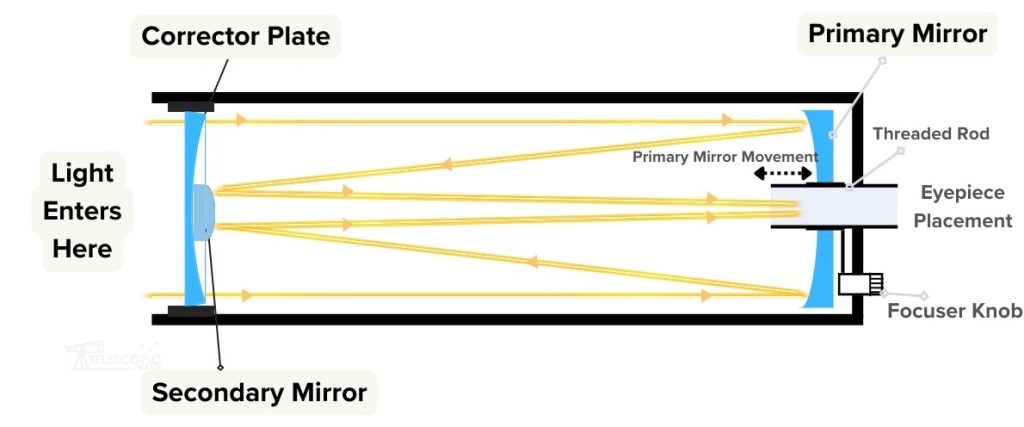
The classical Cassegrain uses a parabolic primary mirror, as in a Newtonian reflector, usually with a fast focal ratio. It also has a hyperbolic secondary mirror with a convex curve to “magnify” the image and send it back towards the primary mirror—usually through a hole in it, unless the telescope is a “Nasmyth” design with a built-in diagonal mirror to redirect the image out the side like a backwards Newtonian reflector
Classical Cassegrains’ parabolic primary mirrors can be used in Newtonians, and some people have made convertible Newtonian/Cassegrain telescopes. I once found a Cassegrain with a damaged secondary mirror and used its primary mirror in one of my Newtonian just fine.
The classical Cass provides sharp images, with little in the way of aberrations for visual use.
The parabolic primary mirror in a classical Cass may not be too difficult to make. But the hyperbolic, convex secondary mirror is extremely difficult to manufacture to tight tolerances and test well.
The Dall-Kirkham Alternative
In the 1940s, Horace Dall and others came up with the Dall-Kirkham Cassegrain, which uses a spherical convex primary mirror and an ellipsoidal primary mirror—essentially an undercorrected parabola, halfway between parabolic and spherical. These are easy to make, very easy to test, and provide sharp images at the center of the field of view.
But they have severe coma, making them essentially useless for anything but planetary viewing/imaging with an accurately tracking mount, or work such as spectroscopy where a wide field of view with sharp stars isn’t required.
Corrected Dall-Kirkhams manufactured today use lenses to compensate for this issue and are great telescopes. But they are not economical to mass-produce at small apertures or attempt to introduce as competition for the well-established Schmidt-Cassegrain design which dominates the amateur market.
The Schmidt Camera and Its Influence
At around the same time as the Dall-Kirkham was created, Bernard Schmidt created a very fast photographic system known as the Schmidt Camera, with a thin, bizarrely curved front corrector lens and a very fast spherical primary mirror. These could produce a photographic focal ratio as fast as f/1.5 at huge apertures and with no optical aberrations over even gigantic photographic glass plates—unheard of at the time and still unusually fast today.
The only catch was that the Schmidt Camera’s focal plane was curved and stuck inside the middle of the telescope. Researchers and aspiring astrophotographers solved this problem by bending the glass plates or film slides to compensate, which isn’t something one can do today with a digital sensor (the exception being the Kepler Space Telescope, which literally used a curved digital sensor array in a Schmidt Camera). This is why systems like Celestron’s RASA or Starizona’s HyperStar exist, with field-flattening lenses.
The Birth of the Schmidt-Cassegrain

It took a few decades, but Tom Johnson, the founder of Celestron, had the idea of combining the Schmidt corrector with the Cassegrain design. Johnson’s stroke of genius was that the Schmidt-Cassegrain can use primary and secondary mirrors with spherical curves, and Schmidt correctors could be mass-produced with what is essentially fancy window glass at a very low cost by creating a “master block” and a series of vacuum presses and grinding/polishing machines to force the glass into the 4th-order curve of the Schmidt corrector. I’ve seen some misguided “DIYers” trying to replace broken Schmidt corrector with flat window glass, only to end up with disastrous results.
A few companies tried to copy Celestron’s process since the 1960s. One (Criterion) went bankrupt in the failed attempt, and a few Japanese enterprises succeeded over the years but never made a profit. Only Meade succeeded but never quite matched Celestron’s quality (and has since gone bankrupt multiple times).
The Schmidt-Cassegrain is technically made with solely spherical mirrors. But in practice, the slight variation of the Schmidt correctors during the manufacturing process means that the secondary mirrors are usually slightly adjusted in their shape to compensate.
Most SCTs use a primary mirror with a focal ratio of around f/2, hence why the HyperStar system turns them into an f/2 instrument. The secondary mirror then magnifies the image by about 5 times, producing a focal ratio of about f/10—the notable exception being Celestron’s C9.25, which uses an f/2.5 primary and a 4x magnifying secondary, contributing to its longer aspect ratio and slightly better image quality.
Focusing Mechanism and Related Optical Challenges
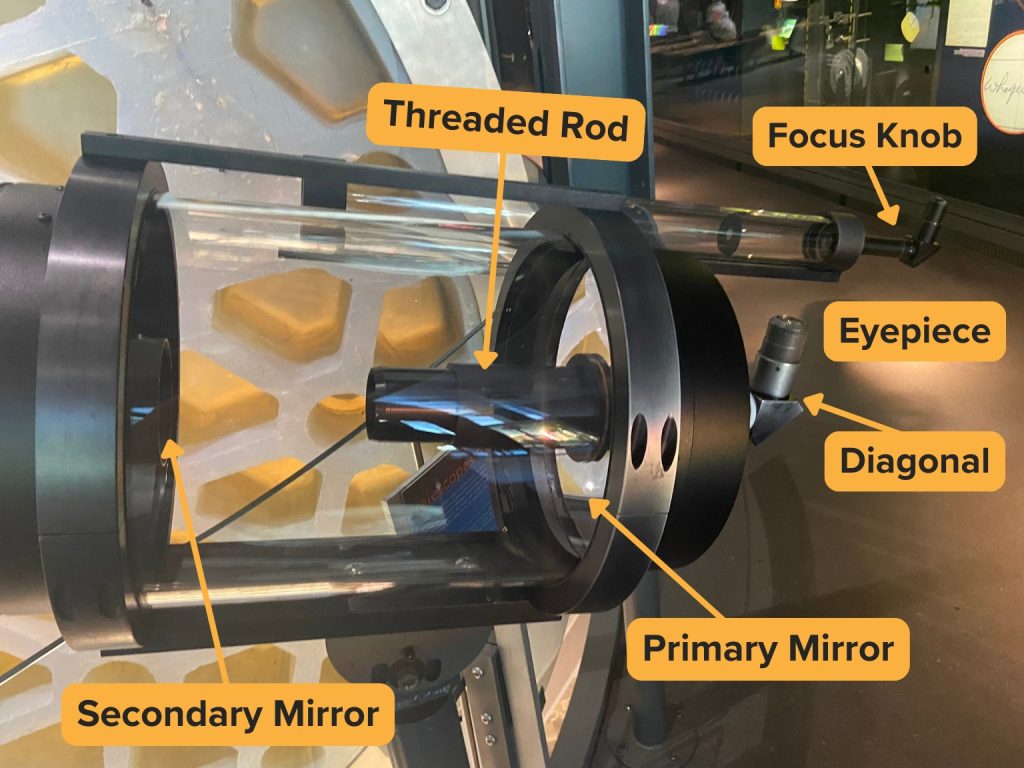
Most SCTs focus by moving the primary mirror along a threaded rod with the turn of a knob, which technically changes the focal length of the whole telescope and can move the focal plane by a large amount with only a small physical adjustment in spacing.
But this focusing mechanism causes issues with the primary mirror wobbling during focusing, which is frustrating at high magnifications or when trying to photograph the planets. The mirror can also “flop” during long exposures, creating star trails. This is why many SCTs meant specifically for imaging have mirror locking knobs. I know many who have drilled holes in their scopes to install locking features themselves, and aftermarket Crayford-style focusers designed to attach to the backs of SCTs are common.
Common Optical Issues in Schmidt-Cassegrains
Schmidt correctors can often have significant defects due to poor quality control, contamination, or physical wear to the master blocks. I’ve especially noticed these in most Criterion and Bausch/Lomb made SCTs, most Celestron and Meade scopes made from 1985-1991 during the astronomy craze surrounding Halley’s Comet, and many of the Meade 16” SCTs.
The 5x “magnifying” nature of the secondary mirror also magnifies collimation errors and defects in the primary mirror, which means that Schmidt-Cassegrains have possibly the worst images of any of the 4 common telescope designs on average. The 4x magnifying secondary in Celestron’s C9.25 is exactly why the scope performs so well; it makes the scope less susceptible to poor images from collimation error and less sensitive to slight figure or cooling issues with the primary mirror.
Because SCTs were designed decades ago and still following fixed standards to this day, they are almost always optimized to deliver large fully-illuminated fields—traditionally sized for a 35mm film slide. So they have big secondary mirrors and big baffles. Most SCTs have central obstructions of 35-40% of the primary mirror diameter, which is enough to significantly impair contrast and even the actual image brightness of the system.

Apart from the issue of central obstruction, the optical issue affecting even the best SCTs is that the field of view is not completely flat; field curvature can appear with some low-power eyepieces and large camera sensors. This is why several companies sell f/6.3 reducer-corrector lenses that both shorten focal length for astrophotography and help flatten the field. However, they are not perfect which is why systems like the Celestron EdgeHD and Meade ACF exist, — both using corrector lenses (like those in the Corrected Dall-Kirkham telescope) to fix field curvature and other minor aberrations.

Thermal Management and Dew Control
With their closed tubes, SCTs can have air currents get trapped in them for long periods of time, impairing sharpness as the warm air slowly escapes on a cold night. This isn’t a problem until you get to large apertures (usually over 11”) or live in an exceptionally cold climate with the scope stored indoors, in which case adding cooling fans and/or vents of some kind might be a good idea.
Conversely, if the corrector plate gets too cold (which is very easy for it to do thanks to how thin it is), it becomes a dew magnet, ruining our views and images until it is warmed up. A dew shield is a necessity for insulating the corrector on most SCTs and also acts like a lens hood to keep stray light out. Dew heaters can be added in addition to a dew shield if need be.
What is a Maksutov-Cassegrain telescope (MCT)?
Key advantages
- Almost impossible to botch the optics, thus leading to great performance
- Little quality variation between units or changes over time
- Sharp images equal or superior to the best refractors with lower cost/weight and no chromatic aberration
- No collimation necessary
- Generally smaller central obstruction than SCTs
- Extremely slow focal ratios—usually f/12 or above—are tolerant of even the worst eyepiece designs
Key disadvantages
- Basically useless for deep-sky astrophotography
- Large Maksutovs are expensive and heavy, and often hard to find
- Cooldown time an issue even with smaller scopes
- Long focal ratio and smaller/narrower baffles mean tiny field of view
The Rise of Maksutov-Cassegrains: From Questar to Mass Market
Maksutov-Cassegrains were invented during World War II by Dmitri Maksutov, but it took Lawrence Braymer and Questar to commercialize the design in the 1950s, along with the telescope’s popularity in telescope-making clubs, for it to take off.
The Questar is renowned for its optical excellence and has been used by NASA and the US Department of Defense for the most rigorous applications. But few attempted to compete with it until the late 1970s, when Celestron attempted to market its C90. C90 was essentially a telephoto lens with a twist-focus design and pretty much no good mounting options. Also the short-lived Quantum series of telescopes was sold by disgruntled former Questar employees. These scopes were still nearly as expensive as the obscenely priced Questar.
In the 1990s, Meade introduced the ETX-90 (originally just ETX). This was a wonderful scope optically, but unfortunately came paired with a crummy finder and plastic mount.
The ETX, along with cheaply imported high-quality Russian-made Maksutovs from Intes and LOMO, paved the way for the birth of Meade and Celestron’s huge lineups of low-quality plastic (but GoTo) telescopes, along with the much lower-cost Maksutov-Cassegrains at other apertures that we know and love today.
Designs and Variations
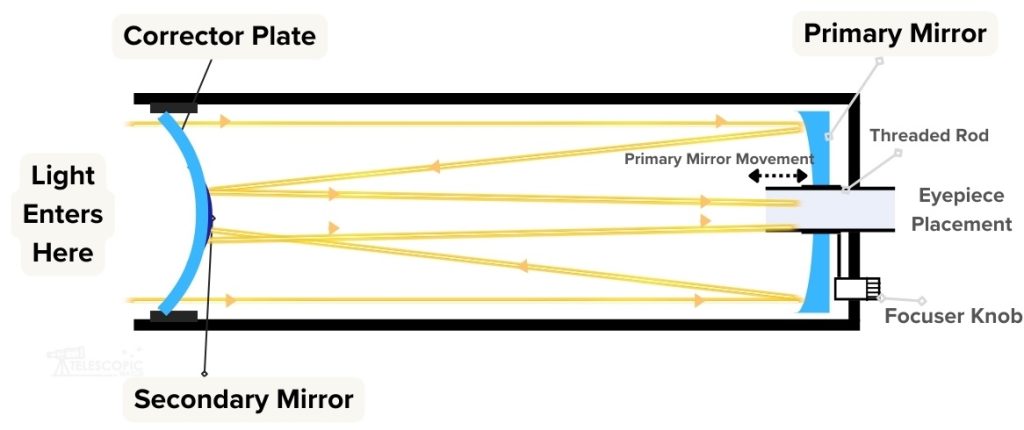
Maksutov-Cassegrains use spherical concave and convex primary and secondary mirrors just like the Schmidt-Cassegrain. However, the corrector lens is a fairly-thick bowl-shaped meniscus lens made out of optical glass, which is spherical itself. It is very easy to manufacture, provided you can mill out big chunks of pricey optical glass.

Many Maksutovs are of the Gregory-Maksutov design, invented by John Gregory, which uses a coated metal “spot” applied to the center of the corrector, as opposed to a separate secondary mirror. This reduces cost and complexity and removes the worry of collimating the secondary.
The downside to Gregory-Maksutov is that damage to the spot coating is basically irreparable. Most manufacturers, as far as I know, won’t service them and no coating company will mask off the corrector just to coat the spot. Unless you attempt to chemically silver it yourself, you’re out of luck.
The few Maksutovs with separated secondary mirrors—usually those made in Russia—are known as Rutten-Maksutovs, though they’re technically just following the original base design.
Due to the price and more precision work involved in making the Maksutov, it wasn’t economical to produce for amateurs until more automated manufacturing facilities became available, combined with cheap overseas labor. This is part of why few Maks larger than about 8-10” exist. Those that do are either specialized research/defense instruments such as 12” Questars owned by NASA or custom amateur scopes like the Stamford Observatory’s 22” Maksutov, which is the largest in the world.
Thermal Management and Dew Control
The other major limitation of making and actually using big Maks is that the thick corrector lens, in addition to the nigh-impossible task of acquiring big enough chunks of crown glass to make them, is inherently a thermal nightmare, soaking up the heat all day and struggling to cool down during the night, producing warped images and huge turbulent air currents as it does so.
Bringing even a 3.5” Maksutov out on a chilly night may require waiting upwards of half an hour for it to cool, and Maksutovs of 6” or above essentially require active cooling or passive reflective insulation wrapped around them regardless of where they are stored or used to function–otherwise they will literally never cool down.
A dew shield and/or heaters as with SCTs are needed to avoid the corrector getting too cold, however, especially if you are using insulation or fans. Some large Maks even have detachable backs to open up the otherwise-closed tube and directly expose the inside and primary mirror to the cool nighttime air.
Unfortunately, the designers of older Maksutovs were not the wisest.
- The Meade 7” Maksutov sold throughout the 2000s has a giant iron counterweight that must be removed from the scope to allow it to function—at the cost of making it unusable on the stock fork mount it comes with.
- The Stamford Observatory 22” has no active or passive cooling systems, an extremely thick primary mirror, a cast-iron mirror cell, and no ventilation besides a tiny hole in the upper tube, and thus delivers sharp images at even the “low” power of 200x roughly once a year when conditions inside and outside the telescope are able to match and the atmosphere itself cooperates.
Common Optical Issues in Maksutov-Cassegrains
While technically not inherent to the design, the vast majority of Maksutov-Cassegrains use identical focusing systems as Schmidt-Cassegrains. But Maksutov’s small apertures reduce the problem of image shift and mirror flop. However, mirror flop is not really a concern, as the Maksutov’s high focal ratios of f/12 or above make deep-sky astrophotography a fruitless endeavor.
Most Maks also have smaller baffles which may not allow the scopes to fully illuminate the field of view of a 2” low-power eyepiece even if they are marketed as working with 2” accessories. This translates to vignetting with DSLRs or cooled astronomy cameras. However, Maks are still wonderful scopes for visual astronomy and planetary imaging, provided you can get them to work and afford one.
The Maksutov is also known as a ‘Brouwer’ after the Dutch optician who invented the same design also during WWII, both Maksutov and Brouwer were recognised as the inventor after the war, as it would have been impossible for both to have had contact during that period of time
Zane,
Being in Tucson now I’m surprised that you didn’t mention the 20″ Vega-Bray Maksutov outside of Benson, near Tucson. I believe that there are a couple other 20″ Maks by other makers, but very few, these things weigh a ton (or very close), not quite suitable for ‘grab and go’ 🙂 .
Never heard of it, is it in an observatory?